Access Control & Security Management
|
GRIDLOCK: A new scalable approach to unifying computer and communications security
|
|
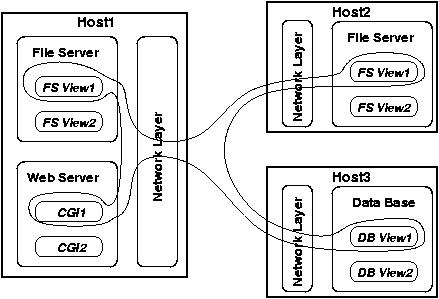
The GRIDLOCK hypothesis is that use of
a globally specified and locally interpreted policy language for
specification of access control policy can provide a new, unified
approach to securing network applications. In particular, this
approach can be used to specify network access control policies and
host access control policies in combination to provide
virtual private services. Virtual Private
Services logically compose the security mechanisms of different system
components (and their policies) to provide a coherent access control
management plane, as shown below.
The Internet architecture scales to large numbers of hosts, and an
increasing number of host types, as a consequence of the
``end-to-end'' rule-of-thumb, which states roughly that functions
which must be performed at endpoints should be performed
there, and not in the network. Security, and more specifically, access
control, being an end-to-end requirement, would be performed at hosts
using the end-to-end model as a design principle. A risk, however, is
that a principle for achieving scalability may cause a tension with
security design principles. In particular, an increasing concern is
the effect that insecure applications (such as mailers and browsers
tightly integrated into host operating systems) can have on other
applications, and further, on hosts elsewhere in the network. Such
applications have been repeatedly exploited.
One approach to the problem of insecure applications damaging networks
is the use of network access control, enforced by a boundary
controller such as an application gateway or firewall. While this
approach is popular and widely deployed, it suffers from three major
problems: (1) firewalls are difficult to administer; (2)
topological restrictions must be used
to ensure that policies are enforced; and
(3) at best, they provide only a rough (and often incorrect)
approximation of the access control desired by
applications. Additional negative effects of firewalls include
interference with routing and congestion control algorithms which are
otherwise rather effective.
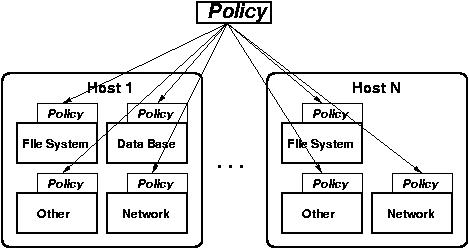
GRIDLOCK is an approach
that, simultaneously, provides more security to applications, greater
scalability, and unification of network access control and host access
control. Policies are specified in a new policy-expression language,
modeled on the KeyNote language we developed for trust management.
This design, like KeyNote,
supports compliance checking, with which
credentials provided by a client can be validated to provide access to
a resource. Our hypothesis is that this approach can be used for both
boundary controllers (where we have some preliminary evidence of
success) and simultaneously in hosts. If we are correct, as this
research is intended to demonstrate, then untrusted code, such as that
attached to e-mails, will be treated as such by the host, as it will
lack any credentials permitting access to anything but the simplest of
host resources. Our belief is that this layer-crossing approach to
security will lead to the creation of a multiplicity of virtual
private services.
Our approach is to combine the development of formal semantics for the
unified access control policy with a rigorous experimental
investigation of the approach, using multiple example
applications.
The GRIDLOCK project is supported by the NSF
Trusted
Computing program, under Contract CCR-TC-0208972.
|
|
|
People
|
Angelos D. Keromytis,
Professor, Computer Science Department, Columbia University
Joan Feigenbaum,
Professor, Computer Science Department, Yale University
Jonathan M. Smith,
Professor, Computer and Information Science Department, University of Pennsylvania
Sheng Zhong (Ph.D. from Yale in 2004), post-doctoral student at DIMACS (will join the faculty at SUNY Buffalo in September 2005)
Sotiris Ioannidis (Ph.D. from U. Penn
in 2005), post-doctoral student at Stevens
Institute of Technology.
James Alexander (Ph.D. student, U. Penn)
Debra Cook (Ph.D. student, Columbia University)
Matthew Burnside (Ph.D. student,
Columbia University)
Michael Locasto (Ph.D. student,
Columbia University)
|
|
|
Publications and Presentations
|
"Towards
a Theory of Data Entanglement (Extended Abstract)"
James Aspnes, Joan Feigenbaum,
Aleksandr Yampolskiy, and Sheng Zhong.
To appear in the Proceedings of
9th European Symposium
On Research in Computer Security
(ESORICS), September 2004, Sophie
Antopolis, France.
"Recursive
Sandboxes: Extending Systrace to
Empower Applications" Aleksey
Kurchuk and Angelos D. Keromytis. In
Proceedings of the 19th
IFIP International Information
Security Conference (SEC), pp. 473
- 487. August 2004, Toulouse, France.
"Distributed Trust" John Ioannidis and
Angelos D. Keromytis. To appear in Practical Handbook of Internet
Computing, ed. Munindar Singh, CRC Press.
"Towards a Theory of Data Entanglement" James Aspnes, Joan Feigenbaum, Aleksandr Yampolskiy, and Sheng Zhong. Yale University Technical Report YALEU/DCS/TR-1277, March 2004.
"Attacks on the (Enhanced) Yang-Shieh Authentication" Ke-Fei Chen and Sheng Zhong. In Computers & Security, vol. 22, no. 8, 2003.
"A Comment on the Chen-Chung Scheme for Hierarchical Access Control" Sehng Zhong and Tianwen Lin. In Computers & Security, vol. 22, no. 5, 2003.
"Managing Access Control in Large Scale Heterogeneous
Networks" Angelos D. Keromytis, Kostas Anagnostakis,
Sotiris Ioannidis, Michael Greenwald, and Jonathan M. Smith. To appear
in the Proceedings of the NATO NC3A Symposium on Interoperable
Networks for Secure Communications (INSC). November 2003, The
Hague, Netherlands.
"EasyVPN: IPsec Remote
Access Made Easy" Mark C. Benvenuto and Angelos
D. Keromytis. In Proceedings of the 17th USENIX
Systems Administration Conference
(LISA), pp. 87 - 93. October 2003, San Diego, CA.
"Verifiable Distributed Oblivious Transfer and Mobile
Agent Security" Sheng Zhong and Yang Richard Yang. In Proceedings of
DialM-POMC, September 2003, San Diego, CA.
"Secure and Flexible Global
File Sharing" Stefan Miltchev, Vassilis Prevelakis,
Sotiris Ioannidis, John Ioannidis, Angelos D. Keromytis, and Jonathan
M. Smith. In Proceedings of the USENIX Annual Technical Conference,
Freenix Track, pp. 165 - 178. June 2003, San Antonio, TX.
"Design and Implementation of
Virtual Private Services" Sotiris Ioannidis, Steven
M. Bellovin, John Ioannidis, Angelos D. Keromytis, and Jonathan
M. Smith. In Proceedings of the IEEE International Workshops on
Enabling Technologies: Infrastructure for Collaborative Enterprises
(WETICE), Workshop on Enterprise Security, Special Session on Trust
Management in Collaborative Global Computing, pp. 269 - 274. June
2003, Linz, Austria.
"WebDAVA: An
Administrator-Free Approach To Web File-Sharing"
Alexander Levine, Vassilis Prevelakis, John Ioannidis, Sotiris
Ioannidis, and Angelos D. Keromytis. In Proceedings of the IEEE
International Workshops on Enabling Technologies: Infrastructure for
Collaborative Enterprises (WETICE), Workshop on Distributed and Mobile
Collaboration, pp. 59 - 64. June 2003, Linz, Austria.
"Experience with the
KeyNote Trust Management System: Applications and Future
Directions" Matt Blaze, John Ioannidis, and Angelos
D. Keromytis. In Proceedings of the 1st International Conference
on Trust Management, pp. 284 - 300. May 2003, Heraclion, Greece.
"Sprite: A Simple, Cheat-Proof, Credit-Based System for Mobile
Ad-Hoc Networks" Sheng Zhong, Jiang Chen, and Yang Richard Yang. In Proceedings of
IEEE INFOCOMM. March/April 2003, San Francisco, CA.
"Requirements for Scalable Access Control and Security Management Architectures" Angelos D. Keromytis and Jonathan M. Smith. Columbia University Computer Science Department Technical Report CUCS-013-02, 2002.
Poster presentation given at the August 2003 Trusted Computing PI meeting
Presentation
given by Joan Feigenbaum at the
PORTIA
Workshop on Sensitive Data in Medical,
Financial, and Content-Distribution
Systems, July 2004 (co-chaired by
Joan Feigenbaum)
June
2004 ITR PI meeting nugget poster
|
|
|
|
|
|