|
One of the primary goals of a filesystem is to efficiently address the portions of
a file by keeping track of where file data is on disk. A multi-level indexed allocation
filesystem like Ext2 provides an efficient mechanism for finding individual disk blocks
based on a byte's position in the file.
Usually, a file does not use its entire available address space or the total number of
disk blocks available to it. Most files are relatively small (on the order of a few
kilobytes of information). The data is logically close in the address space -- it is
clustered in the first few index blocks (although the data may be far apart on the
physical disk).

We create a virtual index by changing the mapping between a byte's position in the file
and the index block it is mapped to. Note that we are not concerned with where the data
is on disk. The data is now unpredictably spread throughout the available address space.
Unix files have long supported an idea like this: file holes. File holes represent unallocated
portions of a file index and return null ('\0') data.
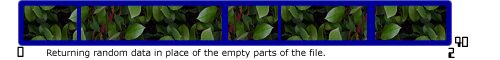
Our technique combines the unpredictable spread of real file data with the dynamic replacement
of consistent random data in place of the file holes created by the virtual index mapping.
Random data is indistinguishable from encrypted data.
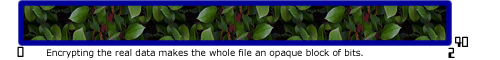
Finally, we encrypt the real file data, thus making it indistinguishable from the random
'camouflage' data in the file holes.
|