|
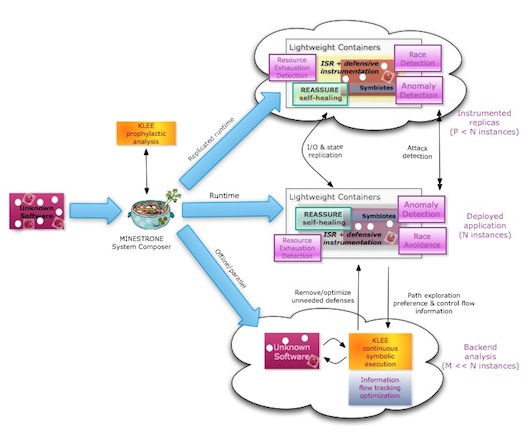
MINESTRONE is a novel architecture that integrates static
analysis, dynamic confinement, and code diversification techniques to enable the
identification, mitigation and containment of a large class of software
vulnerabilities. Our techniques will protect new software, as well as
already deployed (legacy) software by transparently inserting
extensive security instrumentation. They will also leverage concurrent
program analysis (potentially aided by runtime data gleaned from profiling
software) to gradually reduce the performance cost of the instrumentation by
allowing selective removal or refinement.
MINESTRONE will also use diversification techniques for confinement
and fault-tolerance purposes. To minimize performance impact, our project
will also leverage multi-core hardware or (when unavailable) remote servers
to enable the quick identification of potential compromises.
The developed techniques will require no specific hardware or operating
system features, although they will take advantage of such features where
available, to improve both
runtime performance and vulnerability coverage.
Final Project Report:
AFRL-RY-WP-TR-2015-0002.
Contact:
For more information on MINESTRONE contact any of the project's
PIs. For access to software
prototypes please contact
Prof. Salvatore J. Stolfo.
| 

 MINESTRONE Architecture
MINESTRONE Architecture